A new schema policy that enforces which users and teams can modify specific schema resources, closing the gap between file-level CODEOWNERS and object-level DDL access.
GitHub CODEOWNERS enforces who can modify files, but it cannot enforce who can modify schema objects. A developer with access to the inventory/ schema folder could alter the schema to include ALTER TABLE public.users ADD COLUMN, touching a core table owned by another team. The new ownership policy catches this during migration planning and linting, blocking PRs that violate schema boundaries from getting merged.
Configuration
Define ownership rules in your atlas.hcl. Each rule matches schema objects by pattern and specifies which GitHub users or teams are allowed (or denied) to modify them:
lint {ownership "github" {allow "core-tables" {match = "public.*[type=table]"teams = ["backend"]users = ["a8m"]}allow "inventory" {match = "inventory.*"teams = ["data-eng"]}deny "contractors" {match = "*"users = ["contractor-x"]}}}
Rules are evaluated in order. The first matching rule determines access. deny rules take precedence over allow rules for the same resource. Changes that don't match any rule are denied by default. Set default = ALLOW on the ownership block to invert this.
GitHub Teams Integration
When you specify teams in a rule, Atlas uses the GITHUB_TOKEN to call the GitHub Teams API and check membership. Make sure the token has the correct permissions configured. The actor is resolved from the GITHUB_ACTOR environment variable, which is set automatically in GitHub Actions.
PR Feedback
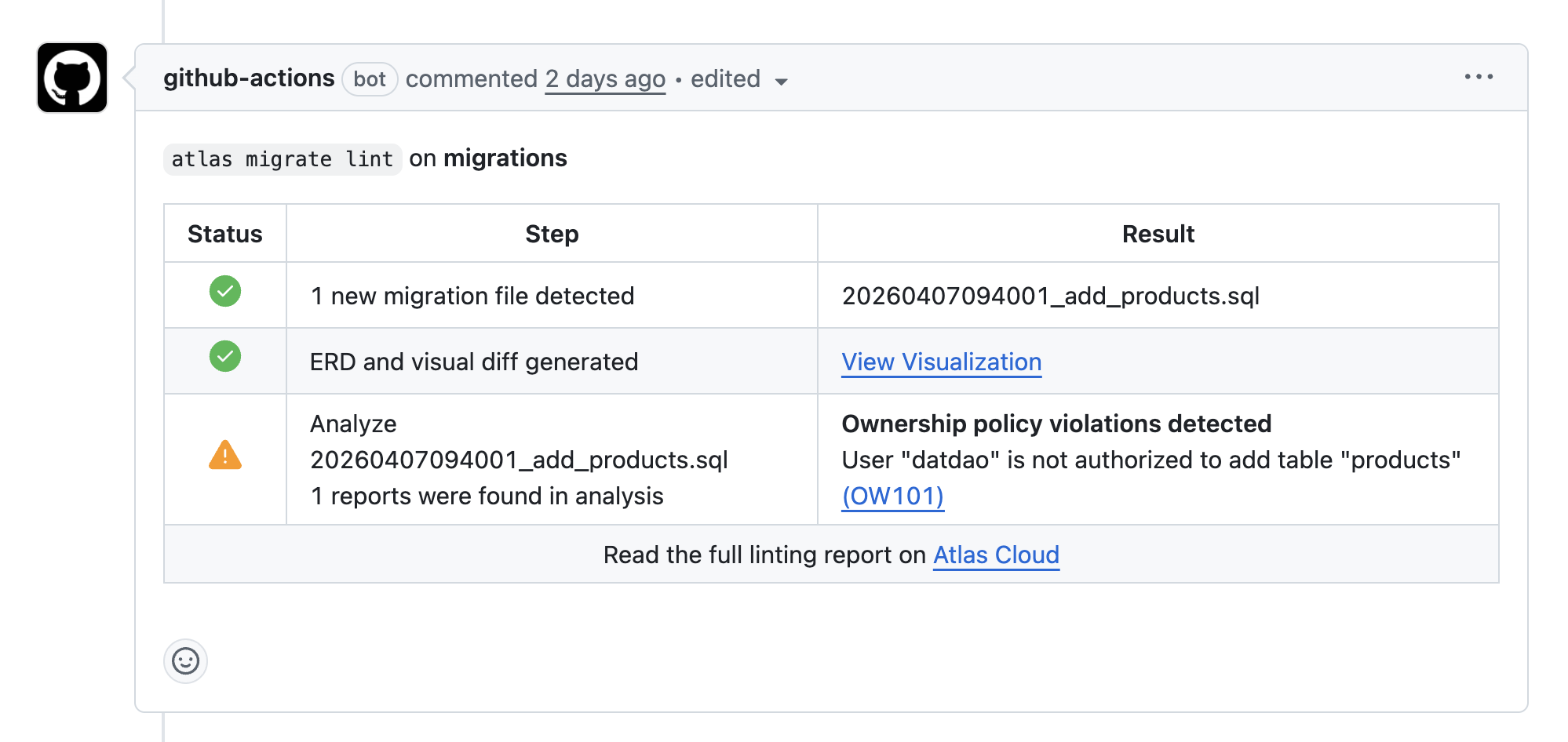
When a violation is detected, Atlas posts a comment on the pull request with the details:
Diagnostic Codes
When a migration violates ownership rules, Atlas reports the violation with a diagnostic code and the rule that triggered it:
-- analyzing version 3-- ownership policy violations detected:-- L3: User "contractor-x" is denied to modify public.table.users (rule "core")https://atlasgo.io/lint/analyzers#OW102-- L7: User "dave" is not authorized to modify inventory.view.stock_levels (rule "inventory")https://atlasgo.io/lint/analyzers#OW101
Two diagnostic codes are reported:
- OW101: User is not authorized to modify the resource (not in any allow list)
- OW102: User is explicitly denied access to the resource
To learn more, see the Ownership Policy documentation.